Post Quantum Cryptography: What It Means for SMEs and How to Prepare
Quantum computing is often discussed as a future problem, but the transition to quantum safe cryptography has already quietly begun.
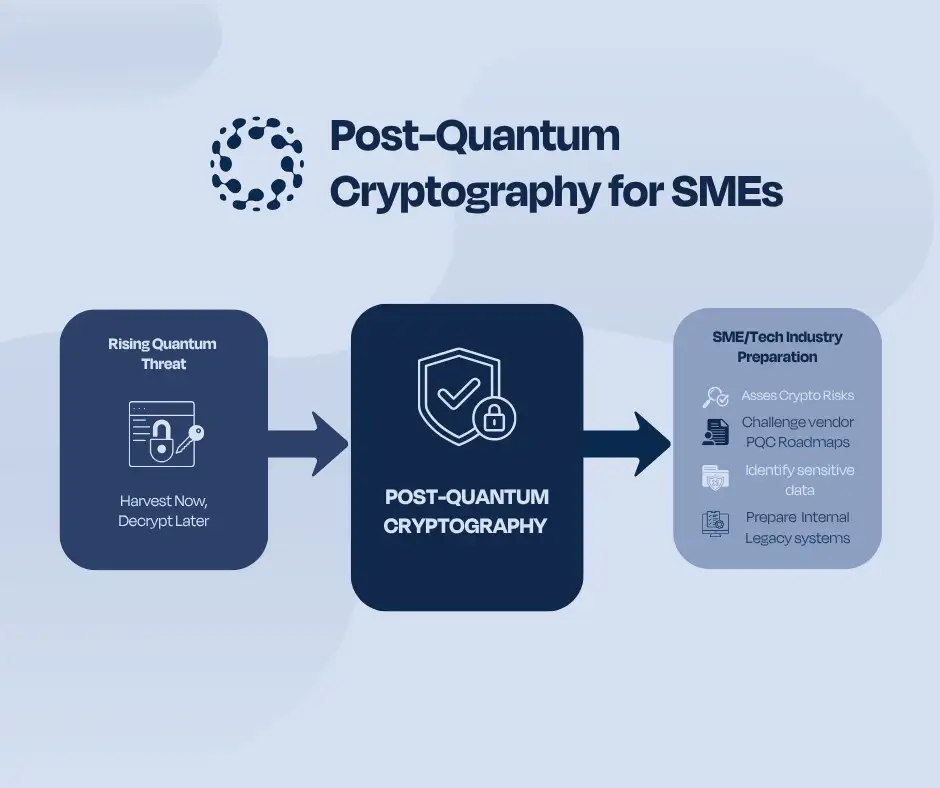
As discussions around post quantum cryptography, quantum computing cyber security, and concepts such as “harvest now, decrypt later” continue to grow, many organisations are asking a practical question. What does this actually mean in practice, especially for SMEs that rely heavily on cloud and third-party technology platforms?
Understanding post quantum cryptography is not about predicting when quantum computers will reach full capability. It is about recognising that the shift towards quantum resilient encryption is already underway, driven by standardisation, early adoption, and increasing regulatory awareness. It is also about recognising that progress in quantum capability may happen faster than currently expected.
What Is Post Quantum Cryptography
To understand what is post quantum cryptography, it helps to start with a simple idea. Most modern digital systems rely on encryption to protect sensitive information such as emails, financial transactions, and stored data.
These encryption methods are secure against current computing power. However, quantum computing introduces a different type of processing capability. In simple terms, quantum computers can solve certain mathematical problems much faster than traditional systems, including those that underpin widely used encryption methods.
Post quantum cryptography refers to cryptographic algorithms designed to remain secure against both classical and quantum attacks. These are often referred to as quantum safe cryptography solutions. A major milestone was reached in August 2024, when NIST finalised the first standardised post-quantum cryptographic algorithms. This provided a foundation for governments and industry to begin transitioning their security infrastructure.
You can explore this work through the NIST post quantum cryptography standards.
At the same time, research indicates that many organisations are still early in their preparation. According to the IBM Quantum Safe Readiness Index 2025, the average organisational readiness score globally is only 25 out of 100.
For SMEs, the key takeaway is that this is no longer theoretical. The transition has already started, but most organisations are still at an early stage.
Why Quantum Computing Is a Risk to Current Encryption
When assessing how will quantum computing affect cyber security, the core issue is that many current encryption methods may become vulnerable. Techniques such as RSA and elliptic curve cryptography underpin secure communications, financial transactions, and data storage. Quantum computing has the potential to break these methods using algorithms that are not feasible today.
This introduces a new category of quantum encryption risks. However, the risk is not only about when quantum computers become capable. It is also about how data is handled today and how long it needs to remain secure.
Regulatory frameworks are already recognising the importance of long-term resilience. The EU Digital Operational Resilience Act overview highlights the need for organisations to manage ICT risks, dependencies, and operational resilience in ways that are also highly relevant to post quantum preparedness.
From a business perspective, encryption is no longer a static control. It must be considered as part of a broader ICT risk management encryption strategy that evolves over time.
What “Harvest Now, Decrypt Later” Means in Practice
One of the most discussed quantum computing risks for businesses is often referred to as harvest now decrypt later explained in practical terms. The concept is simple. An attacker may collect encrypted data today, even if they cannot decrypt it. That data can then be stored and decrypted later when quantum computing capabilities improve.
This creates a long-term data encryption risk that is particularly relevant for certain types of information.
Examples include:
- Intellectual property such as product designs, algorithms, and strategic plans that retain value for many years
- Financial data and transaction records that are subject to retention requirements
- Regulated information such as personal data and compliance documentation
In each case, the concern is not just about protecting data today. It is about ensuring that it remains secure throughout its lifecycle. This shifts the focus from immediate threats to long term exposure, which is a key consideration in quantum computing cyber security discussions.
What This Means for SMEs and Businesses
For many SMEs, cryptography is not implemented directly within their own systems. Instead, it is embedded within the technology platforms they rely on, including cloud providers, operating systems, identity platforms, and security services.
Major providers such as Microsoft, AWS, Google, Cloudflare, and several others are already preparing for the transition. Some early adoption is visible, with providers such as Google and AWS beginning to integrate post quantum cryptography into parts of their infrastructure, often using hybrid approaches. Platforms such as Signal have also begun deploying quantum resistant protocols in practice.
This reinforces an important point. Post quantum cryptography for SMEs is not something they will build themselves. It will largely be delivered through the technology ecosystem. However, this does not mean organisations can ignore the transition.
Even where cryptography is largely handled by technology providers, businesses should still:
- Maintain visibility over where cryptography is used across systems and applications
- Identify long lived sensitive data that may require protection over extended periods
- Monitor and actively challenge vendor readiness, including whether key providers have a PQC roadmap, which services will transition first, whether they support crypto agility, and whether they provide clear timelines for moving away from vulnerable algorithms
- Understand risks arising from legacy systems and internally developed applications, particularly where cryptography is embedded in code or depends on libraries that may not easily support future upgrades
A key concept here is crypto agility. This refers to the ability to quickly update or replace cryptographic algorithms without disrupting systems. Organisations that lack this flexibility may face greater challenges during the transition.
The Hidden Risk: Vendor and Cloud Dependency
A significant risk for many organisations lies in their dependency on third party providers. Most businesses rely on external platforms for core operations, including data storage, communication, and transaction processing. These platforms manage encryption on behalf of the organisation.
This creates a dependency that can obscure risk. If a provider is slow to adopt quantum safe cryptography or lacks a clear transition strategy, the organisations relying on that provider may inherit that exposure.
This is where ICT risk management encryption becomes critical. It is not only about internal controls but also about understanding how vendors manage cryptographic risk. Structured approaches such as ICT risk management and regulatory compliance can help organisations build visibility over their technology environment. Similarly, implementing third party risk assessment frameworks supports the evaluation of vendor dependencies and resilience. supports the evaluation of vendor dependencies and resilience.
The challenge is not purely technical. It requires governance, oversight, and active engagement with providers.
Governance and Regulatory Perspective
From a governance perspective, post quantum cryptography is increasingly relevant.
Frameworks such as DORA already require organisations to maintain visibility over ICT assets, dependencies, certificates, and cryptographic controls. They also place strong emphasis on third party risk management and oversight.
At the same time, regulatory focus is evolving. Authorities are beginning to assess how organisations are preparing for future cryptographic risks. For example, the MFSA has included post quantum readiness within its supervisory priorities, signalling growing supervisory expectations around cryptographic resilience and legacy system risk.
This aligns with broader requirements under AML and risk management frameworks and data protection and compliance requirements, where organisations must identify, assess, and mitigate risks that could impact data integrity and confidentiality.
Quantum computing does not introduce entirely new regulatory obligations. Instead, it reinforces the importance of applying existing governance principles to emerging risks.
How to Start Preparing for Quantum Safe Cryptography
Preparing for quantum safe cryptography does not require immediate implementation. However, organisations should already be assessing exposure and planning for the transition.
A practical starting point includes the following steps;
- Identify where cryptography is used across systems, applications, and third-party services
- Assess long lived sensitive data that may require protection for several years
- Review vendor readiness, including whether providers have a PQC roadmap, support quantum safe cryptography and crypto agility, and communicate transition plans for key services
- Identify risks in legacy systems and internally developed applications
These actions should be supported by clear governance structures. Developing internal policies and procedures can help ensure consistency and accountability.
Where internal resources are limited, organisations may also consider outsourcing compliance and risk functions to access specialised expertise.
For most SMEs, much of the technical transition will occur through their technology providers. However, organisations are still responsible for understanding their exposure and managing associated risks.
Final Thoughts
Post quantum cryptography may still feel like a future issue. However, with new standards and guidance emerging, major technology providers preparing, early adoption already visible, and the risk of faster-than-expected progress in quantum capabilities, the transition to quantum safe security has effectively begun.
SMEs should therefore begin preparing accordingly by reviewing their exposure to future cryptographic risks and embedding quantum readiness into their wider risk, resilience, and technology planning.
